- Home
- Investigations
- Kenneth John Arellano

Kenneth John Arellano
Threat Alert- Investigation status
- Ongoing
We are investigating Kenneth John Arellano for allegedly attempting to conceal critical reviews and adverse news from Google by improperly submitting copyright takedown notices. This includes potential violations such as impersonation, fraud, and perjury.
- Company
-
LPL Financial
- City
-
Rochester
- Country
-
NY
- Allegations
-
Incomplete records

- https://lumendatabase.org/notices/73789261
- https://lumendatabase.org/notices/73791163
- https://lumendatabase.org/notices/73532628
- https://lumendatabase.org/notices/73641069
- https://lumendatabase.org/notices/73644255
- https://lumendatabase.org/notices/73588056
- https://lumendatabase.org/notices/73531487
- https://lumendatabase.org/notices/73523610
- Jim Fung
- [REDACTED]
- Jim Fung
- Michael Collette
- David Roots
- Elroy Stansel
- David Roots
- Fabian Carson
- https://adviserinfo.sec.gov/firm/summary/152043
- https://brokercheck.finra.org/individual/summary/2660786
- https://www.voterfocus.com/CampaignFinance/candidate_pr.php?op=cv&e=14&c=indian&ca=377&rellevel=4&committee=N
- https://brokercheck.finra.org/individual/summary/2660786
- https://adviserinfo.sec.gov/individual/summary/2660786
Evidence Box and Screenshots





1 Alerts on Kenneth John Arellano
- RED FLAGS
Kenneth John Arellano and His Impact
Explore the controversial history of Kenneth John Arellano in wealth management and investment advising since 1996.
Visit LinkHow Was This Done?
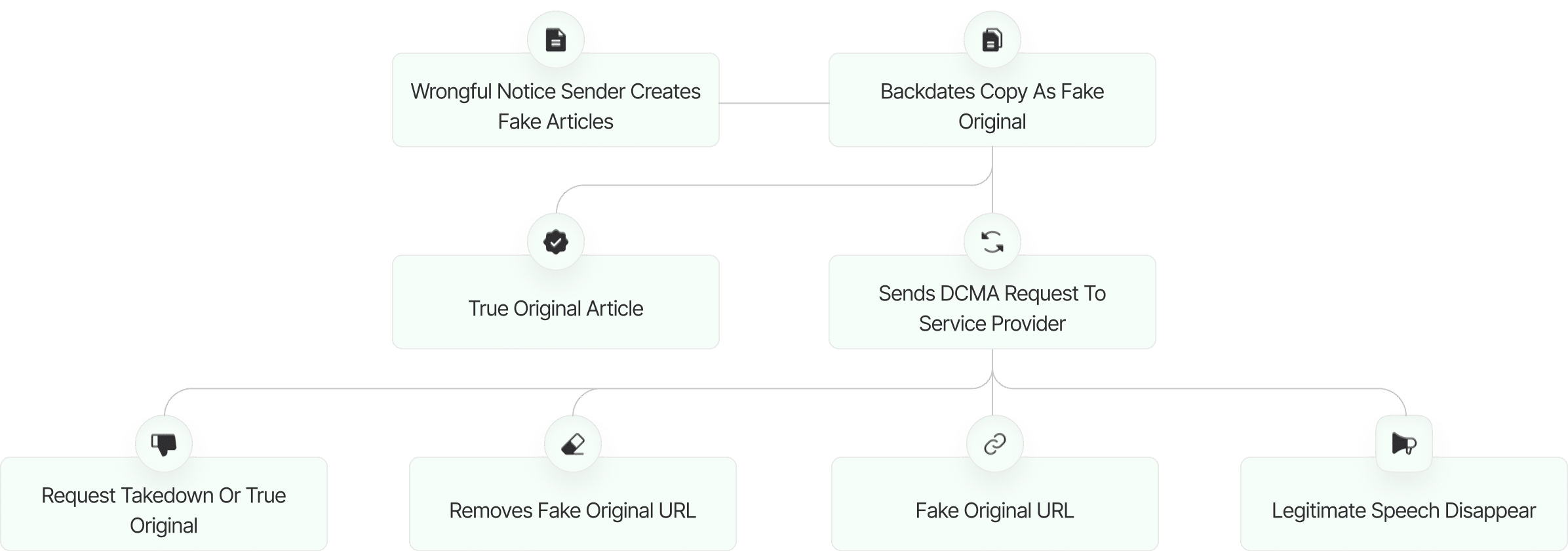
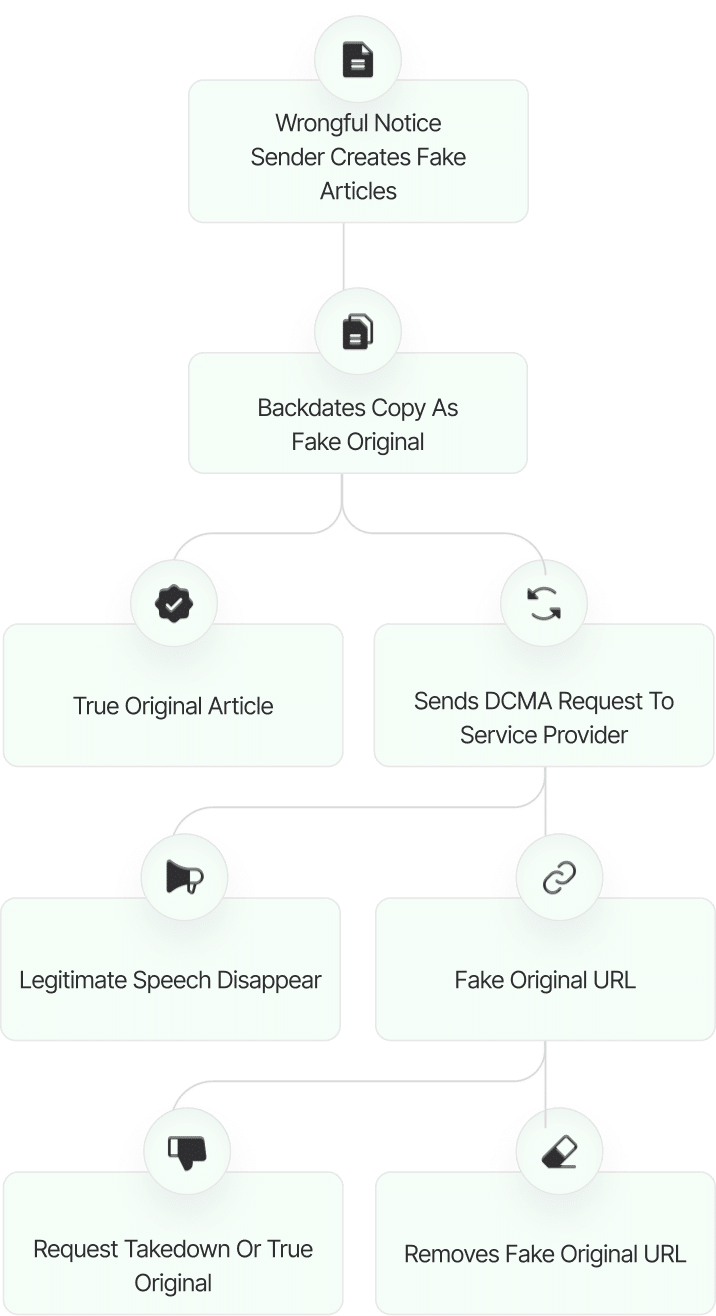
The fake DMCA notices we found always use the ? back-dated article? technique. With this technique, the wrongful notice sender (or copier) creates a copy of a ? true original? article and back-dates it, creating a ? fake original? article (a copy of the true original) that, at first glance, appears to have been published before the true original.
What Happens Next?
The fake DMCA notices we found always use the ? back-dated article? technique. With this technique, the wrongful notice sender (or copier) creates a copy of a ? true original? article and back-dates it, creating a ? fake original? article (a copy of the true original) that, at first glance, appears to have been published before the true original.
01
Inform Google about the fake DMCA scam
Report the fraudulent DMCA takedown to Google, including any supporting evidence. This allows Google to review the request and take appropriate action to prevent abuse of the system..
02
Share findings with journalists and media
Distribute the findings to journalists and media outlets to raise public awareness. Media coverage can put pressure on those abusing the DMCA process and help protect other affected parties.
03
Inform Lumen Database
Submit the details of the fake DMCA notice to the Lumen Database to ensure the case is publicly documented. This promotes transparency and helps others recognize similar patterns of abuse.
04
File counter notice to reinstate articles
Submit a counter notice to Google or the relevant platform to restore any wrongfully removed articles. Ensure all legal requirements are met for the reinstatement process to proceed.
05
Increase exposure to critical articles
Re-share or promote the affected articles to recover visibility. Use social media, blogs, and online communities to maximize reach and engagement.
06
Expand investigation to identify similar fake DMCAs
Widen the scope of the investigation to uncover additional instances of fake DMCA notices. Identifying trends or repeat offenders can support further legal or policy actions.
Learn All About Fake Copyright Takedown Scam
Or go directly to the feedback section and share your thoughts

Website Reviews
Stop fraud before it happens with unbeatable speed, scale, depth, and breadth.
Recent Reviews

Cyber Investigation
Uncover hidden digital threats and secure your assets with our expert cyber investigation services.
Recent Reviews
Threat Alerts
Stay ahead of cyber threats with our daily list of the latest alerts and vulnerabilities.
Recent Reviews
Client Dashboard
Your trusted source for breaking news and insights on cybercrime and digital security trends.
Recent Reviews
Payomatix
Fake DMCA Investigation
Ruchi Rathor
Fake DMCA Investigation
Gamsgo
Fake DMCA Investigation
User Reviews
Discover what real users think about our service through their honest and unfiltered reviews.
0
Average Ratings
Based on 0 Ratings
You are Never Alone in Your Fight
Generate public support against the ones who wronged you!
Featured Cyber Investigations
Explore our most impactful cyber investigations, where we uncover coordinated digital deception, expose fraudulent takedown schemes, and reveal the hidden mechanics behind online manipulation.
Payomatix
Fake DMCA Investigation
Ruchi Rathor
Fake DMCA Investigation
Gamsgo
Fake DMCA Investigation
FXNovus
Fake DMCA Investigation
Claudio Teseo
Fake DMCA Investigation
KTV Group...
Fake DMCA Investigation
Emarlado.com
Fake DMCA Investigation
GoodSkin Clinics
Fake DMCA Investigation