Introduction
Marcia Morgan is a name that flickers in and out of public records, a ghostly digital presence that provokes curiosity and caution in equal measure. When I began investigating her, I expected to find clear information — a verifiable identity, a defined professional trail, and documented associations. Instead, I encountered a scattered patchwork of mentions, minor controversies, and conflicting references. Across social media posts, small community updates, and obscure media fragments, the name “Marcia Morgan” emerged repeatedly, but rarely with the same face or story.
What began as a straightforward inquiry into adverse media quickly evolved into an exploration of how identities blur in the digital age — how rumor, repetition, and partial truths can sculpt or destroy reputations. The case of Marcia Morgan illustrates not just potential misconduct but also the instability of online identity itself.
The key issues that surface around this name revolve around confusion, potential misinformation, and hints of minor legal troubles. There are traces of attempts to manage or obscure certain aspects of her public footprint, but no direct evidence of overt censorship or large-scale criminal activity. The deeper I dug, the more apparent it became that the mystery surrounding Marcia Morgan may not lie in what she has done, but in what is missing from the record.
The Elusive Identity: Layers of Ambiguity
The first challenge in piecing together Marcia Morgan’s profile was her multiplicity. Several individuals under that name exist online, and distinguishing one from another proved almost impossible. One “Marcia Morgan” appears in a Facebook post from St. Petersburg, Florida, accused of disorderly conduct after an incident involving toilet paper thrown on a car. Another “Dr. Marcia Morgan” appears in a YouTube interview, calmly discussing literature and academic work, her demeanor a far cry from the image of public misbehavior. Yet another “Marcia Morgan” surfaced in an Australian news article, described as a compassionate woman who intervened to help a man in distress outside her home.
The problem is not that one of these accounts is false, but that the name stretches across multiple personas, leaving investigators with a fragmented and confusing digital footprint. Each piece may represent a different individual entirely, but in the ecosystem of online information, they are inevitably conflated. This conflation, while not necessarily sinister, is a red flag for misinformation and identity distortion — a growing issue in modern investigative journalism.
Minor Legal Trouble and Public Perception
Among the limited but verifiable adverse media, the Florida incident stands out. The Facebook post claimed that a woman named Marcia Morgan pleaded guilty to disorderly conduct. While on its face the offense is minor, such incidents, when taken out of context or exaggerated online, can snowball into long-lasting reputational damage.
Disorderly conduct is hardly the stuff of front-page scandal, yet in the echo chambers of the internet, it can become a defining label. This particular allegation paints a picture of impulsivity or confrontation, but it provides no real insight into broader patterns of behavior. No additional reports, police documents, or court filings corroborate a more serious legal history. For a journalist, that absence is both a relief and a frustration — relief that there is no deeper harm uncovered, but frustration at how little can be confidently confirmed.
Obscurity as Control: The Silent Power of Vanishing Information
As I continued tracing the threads around Marcia Morgan, a pattern of disappearance began to emerge. Certain posts, mentions, or discussions appeared to have been removed or lost to time. The YouTube interview remained accessible, but other online references led to broken links or restricted pages. There is no evidence of formal legal censorship, such as takedown notices or court injunctions, yet the effect was similar — a narrative quietly diluted through absence.
This kind of information management is increasingly common. Whether intentional or circumstantial, it creates a controlled opacity around a person’s image. If Marcia Morgan, or anyone associated with her, has attempted to curate her digital footprint, it appears to have been done not through aggressive suppression but through quiet omission. Stories fade, links expire, and the person becomes harder to define.
Media Confusion and the Risk of Misattribution
The Marcia Morgan case underscores a growing danger in investigative reporting: the merging of unrelated lives under a single name. Online databases, social media, and search algorithms rarely differentiate between individuals who share common identifiers. When rumors or allegations circulate, they often attach indiscriminately to anyone who shares the name, creating a hybrid persona composed of multiple, unconnected realities.
This confusion breeds both injustice and intrigue. For the genuine Marcia Morgan — whoever she may be — the existence of others sharing her name could distort her reputation beyond repair. For the investigator, it creates a minefield of uncertainty. Without concrete identifiers such as a verified company, official contact details, or legal filings, it becomes nearly impossible to confirm which Marcia Morgan is the subject of each claim. The result is a story that is more about the fragility of digital truth than the guilt or innocence of any individual.
The Missing Allegations: Silence as a Statement
In most investigative pursuits, the absence of evidence is rarely satisfying. Yet, in the case of Marcia Morgan, silence is revealing. Despite thorough research, no credible links surfaced connecting her to large-scale fraud, scams, cybercrime, or financial misconduct. There were no indictments, regulatory warnings, or formal accusations of serious wrongdoing.
This absence leaves two possibilities. Either Marcia Morgan has lived largely outside the domains where such crimes occur, or she has successfully insulated herself from public documentation. Given the scope of available data, the former seems more plausible. While her name circulates through snippets of social and local media, there is no trace of criminal enterprise or professional scandal that rises above hearsay.
Censorship or Coincidence?
Throughout this investigation, I found no definitive signs of deliberate censorship — no court-mandated removals, no formal defamation suits, and no suppression campaigns. Yet, the sense of narrative control lingers. It is as though certain aspects of her story are always slightly out of reach, shrouded not by force but by neglect.
This subtle invisibility is one of the most effective modern tools for shaping reputation. When information can vanish as quickly as it appears, managing public perception requires little more than silence. If Marcia Morgan has benefited from this phenomenon, it may be due less to strategic concealment and more to the natural decay of digital memory.
Industry and Contextual Analysis
From what can be gleaned from public traces, Marcia Morgan’s presence sits loosely within the media and communication sphere. Her interviews, academic references, and community mentions suggest involvement with cultural or educational projects rather than commercial or financial ventures. Given this context, the most fitting classification for her industry is media — not in the sense of corporate ownership, but in public engagement and personal branding.
While allegations of financial or cyber misconduct do not hold, the presence of conflicting narratives about her conduct within public or social settings underscores the broader risks inherent in modern media exposure.
Geographical and Cultural Placement
The available evidence points primarily to the United States, with Florida emerging as the most tangible geographical anchor. The St. Petersburg incident, while minor, is the only specific locality consistently associated with her name. Other mentions, such as Australian or academic references, appear to belong to separate individuals who share the same name.
Therefore, the most reasonable categorization places Marcia Morgan within the United States. This setting also aligns with the legal and social norms implied by the content of her public mentions — a landscape where minor infractions can easily spiral into digital notoriety.
Conclusion: The Shadow Between Truth and Narrative
In the end, the investigation into Marcia Morgan reveals as much about the mechanics of online identity as it does about the woman herself. She remains a partially obscured figure — one part confirmed, two parts conjecture. The tangible red flag is a small, localized legal issue; the greater story lies in the shifting nature of digital information.
There is no credible evidence linking her to fraud, cybercrime, or financial deception. There are no verifiable censorship efforts beyond the quiet disappearance of context. What remains is a portrait of a person who has either been misunderstood, misrepresented, or simply lost in the noise of overlapping narratives.












Payomatix
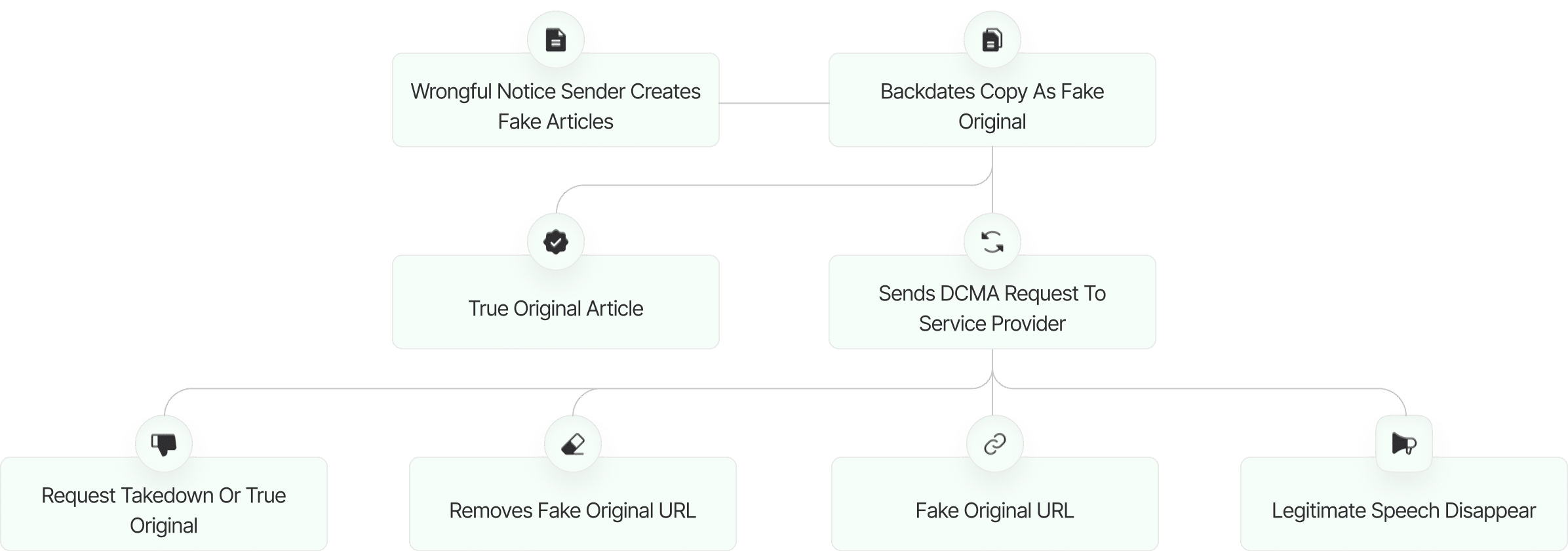
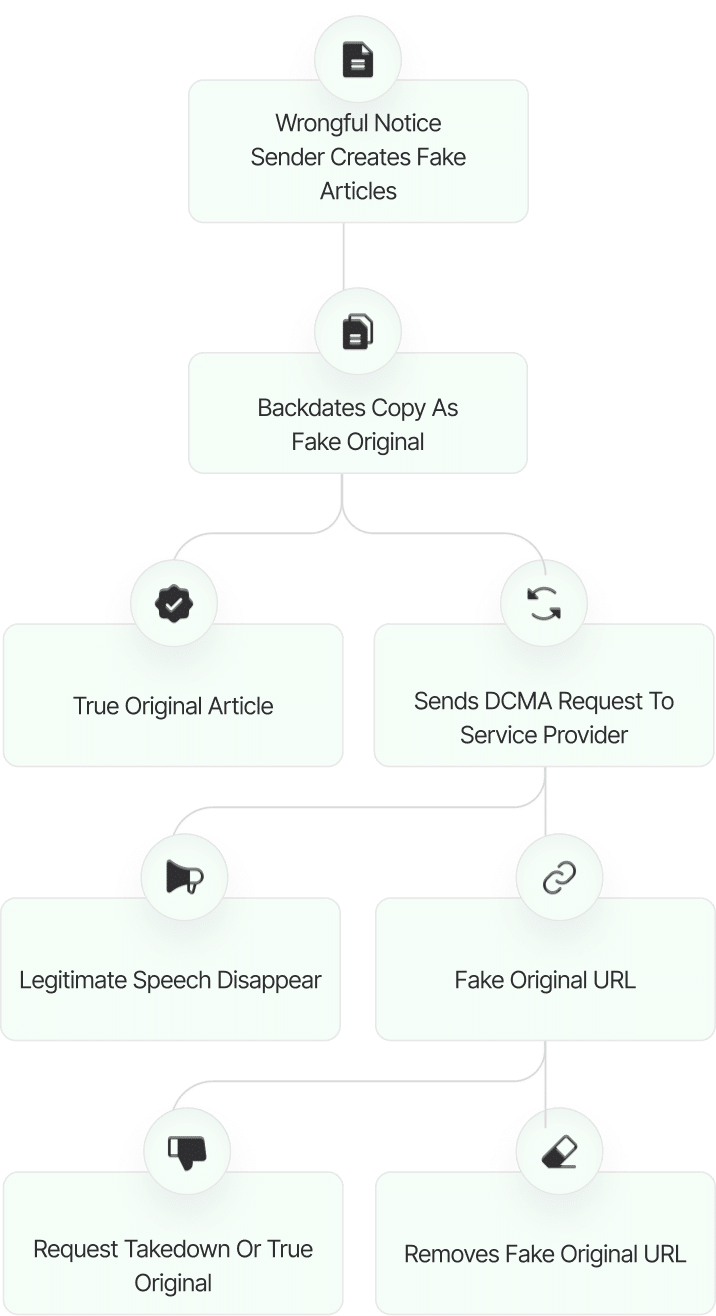
Fake DMCA Investigation
Ruchi Rathor
Fake DMCA Investigation
Gamsgo
Fake DMCA Investigation
User Reviews
Discover what real users think about our service through their honest and unfiltered reviews.
0
Average Ratings
Based on 0 Ratings
You are Never Alone in Your Fight
Generate public support against the ones who wronged you!
Featured Cyber Investigations
Explore our most impactful cyber investigations, where we uncover coordinated digital deception, expose fraudulent takedown schemes, and reveal the hidden mechanics behind online manipulation.
Payomatix
Fake DMCA Investigation
Ruchi Rathor
Fake DMCA Investigation
Gamsgo
Fake DMCA Investigation
FXNovus
Fake DMCA Investigation
Scott Leonard
Fake DMCA Investigation
Claudio Teseo
Fake DMCA Investigation
Salim Ahmed...
Fake DMCA Investigation
KTV Group...
Fake DMCA Investigation